Windows LAPS Compared
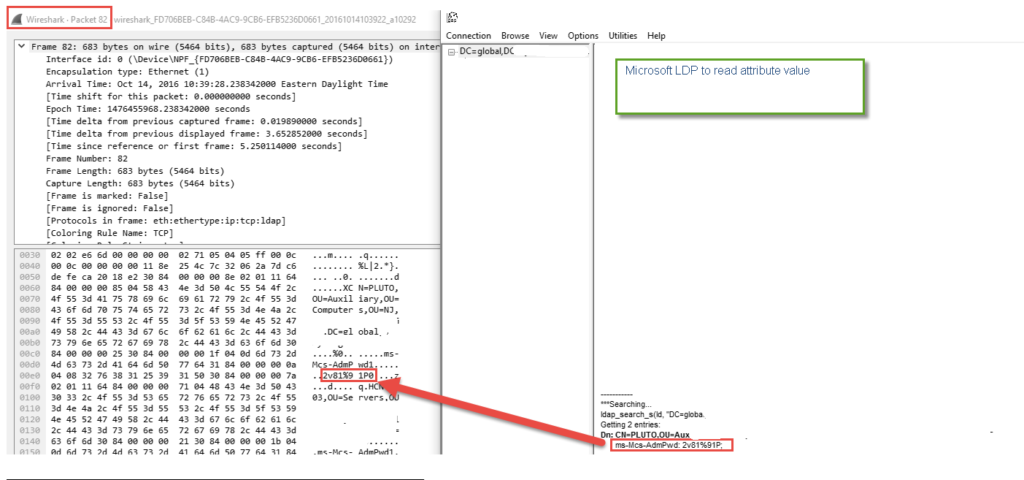
Pass-the-Hash (PtH) attacks against the Windows operating systems are becoming common. Microsoft wants organizations to assume that a breach has already occurred in order to highlight the need for a more mature defense. This article helps organizations plan their strategies for a more effective defense against pass-the-hash attacks.
With AD Client Extensions software installed, the Local Administrator Password is system generated and unlike Windows LAPS, it is stored in Active Directory in encrypted form. No AD Schema Changes are required, and password can be stored in custom application partition thus allowing control over the replication to specific and physically well secured DCs. Passwords are validated regularly and reset to maintain their integrity. Only designated administrators are allowed to decrypt the password strings.
The feature was first launched in ADCE 2012 and has matured significantly over the past years making it a proven solution for large enterprise customers.
Limited Time Offer on Software Subscription.
The Ultimate Windows Extensions
For offer details, write to sales@synergix.com
The Ultimate Windows Extensions
THE CHOICE IS CLEAR
Non MAPS* related features
Multiple Account Password Solution
MAPS
Multiple Account Password Solution
Managed Accounts
Azure AD Domain Services
No Active Directory Schema Changes
Centralized Auditing
Strictly follow Principle of Least Privileges
Domain Admins exclusion
Encrypted Password
Unique Encryption Key
Limit Replication Scope using Application Partition
Store data in other objectClass ex.associated Device object
Password Masking
Tamper resistant password
RDP to target by masking username and password
Rename Local Administrator Account regularly
Rename Backup (non S-500) Admin Account regularly
Confidential Attribute without Schema Extensions
Require input of business reason before retrieving password
Password Aging after checkout
Windows 7.0 SP1 to Windows Server 2019 support
Windows XP and Windows Server 2003 Support
Strategic Solution